
Technology has become a major part of everyday life from online payments and education to entertainment and communication. With so much personal and business information stored digitally, security has become more important than ever. Ethical hacking is the practice of legally testing computer systems, networks, or applications to find security weaknesses before criminals can misuse them. Unlike illegal hacking, ethical hacking is done with permission and follows strict legal and professional guidelines. The main goal is protection, not harm. Ethical hackers act as digital security testers who help organizations identify risks early and fix them before they turn into serious problems. This proactive approach makes the online world safer for individuals, businesses, and governments.
Ethical hackers are trained cybersecurity professionals who understand how hackers think but use their knowledge responsibly. Many experts gain certifications from organizations like EC-Council, which trains professionals in ethical hacking skills and cybersecurity practices. Their responsibilities often include testing security systems, checking networks for vulnerabilities, reviewing software safety, and suggesting improvements. Ethical hackers work with IT teams to strengthen defenses and ensure sensitive data remains protected. They don’t just find problems they help solve them. This makes their role essential in companies that handle financial information, customer data, healthcare records, or confidential business details.
Cyber attacks are increasing every year, targeting both individuals and large organizations. Technology companies like Google and IBM invest heavily in cybersecurity because even a small data breach can lead to huge financial losses and damage to reputation. Ethical hacking helps organizations stay ahead of threats by identifying weaknesses before criminals do. It also helps protect customer privacy, maintain trust, and ensure smooth digital operations. As businesses continue moving online, cybersecurity and ethical hacking specifically is becoming a basic necessity rather than an optional investment.
Ethical hacking follows a structured and legal process. First, the organization gives official permission to test its systems. Then ethical hackers use professional tools and techniques to simulate possible cyber attacks in a controlled environment. This may include checking network security, testing website vulnerabilities, analyzing system configurations, and evaluating human-related security risks like weak passwords. After testing, they prepare detailed reports explaining what weaknesses were found and how they can be fixed. Companies then use this information to strengthen security systems. This preventive approach reduces the chances of future cyber attacks and helps organizations stay secure in an evolving digital landscape.
Ethical hacking directly affects the safety of everyday digital activities. Social media platforms, online banking apps, shopping websites, and even government services rely on strong cybersecurity measures. Companies such as Meta Platforms regularly employ ethical hackers to test security and protect user data. Without ethical hacking, cybercrime could increase significantly, leading to financial fraud, identity theft, and loss of sensitive information. By identifying vulnerabilities early, ethical hackers help build safer digital environments, maintain trust in technology, and ensure that people can confidently use online services. As digital transformation continues worldwide, ethical hacking will remain one of the key pillars of cybersecurity.
One of the most common misunderstandings about ethical hacking is that it involves illegal or questionable behavior. Many people hear the word “hacking” and immediately associate it with cybercrime, data theft, or system breaches. However, ethical hacking is completely legal when done with proper authorization. Ethical hackers are hired specifically to test systems in a controlled and responsible way. They follow professional codes of conduct and often receive training from recognized organizations such as EC-Council, which focuses on ethical cybersecurity education. Their goal is not to harm but to protect, ensuring digital systems remain safe and trustworthy.
Another widespread myth is that ethical hackers and malicious hackers are essentially the same. While they may use similar technical tools and knowledge, their intentions and legal boundaries are completely different. Criminal hackers aim to exploit vulnerabilities for personal gain, disruption, or unauthorized access. Ethical hackers, in contrast, work with permission to strengthen security. Their role is preventive they identify risks early so organizations can fix them before attackers cause damage. This difference in purpose is what truly separates ethical professionals from cybercriminals.
Many beginners hesitate to explore ethical hacking because they assume it requires extraordinary technical genius. While cybersecurity certainly involves learning technical skills, most professionals build their expertise step by step. Foundational knowledge in networking, operating systems, and basic security practices often comes first. Over time, curiosity, practice, and continuous learning help individuals grow in the field. Passion for problem-solving and persistence are often more valuable than natural brilliance. Ethical hacking is a skill that can be developed with dedication rather than something reserved only for tech prodigies.
There is a common belief that ethical hacking only matters for large corporations or major tech companies. In reality, any organization or individual using digital platforms can be a target. Small businesses, educational institutions, startups, and even personal websites face cybersecurity risks. Companies like Google invest heavily in cybersecurity, but smaller organizations also need protection to safeguard customer data, financial transactions, and business operations. Ethical hacking helps organizations of all sizes strengthen their defenses and reduce potential risks.
Some people assume that once ethical hacking is performed, systems become permanently secure. Unfortunately, cybersecurity doesn’t work that way. Technology constantly evolves, and new vulnerabilities can emerge over time. Ethical hacking significantly improves security, but it is not a one-time solution. Continuous monitoring, regular testing, updates, and employee awareness are all necessary to maintain strong protection. Ethical hacking should be seen as an ongoing process that adapts alongside emerging cyber threats.

When most people hear the word hacker, they often imagine someone secretly breaking into systems or stealing data. But in reality, hacking is a broad field with many different categories of hackers, each defined mainly by their intentions, ethics, and legality. Understanding these types is important because it helps separate myths from reality and shows how ethical hacking plays a positive role in cybersecurity. Not all hackers are criminals some actually work to make the digital world safer.
White hat hackers, often called ethical hackers, are cybersecurity professionals who use their skills legally to protect systems rather than exploit them. Organizations hire them to test security measures, identify vulnerabilities, and suggest improvements before malicious hackers can attack. Their work helps safeguard sensitive data, prevent cybercrime, and strengthen digital trust. Ethical hackers operate with permission, follow professional guidelines, and prioritize security over personal gain. They are essential in today’s world where businesses, governments, and individuals depend heavily on digital infrastructure.
Black hat hackers are individuals who use hacking techniques for illegal or harmful purposes. Their goals may include financial theft, data breaches, identity fraud, or disruption of services. These hackers often exploit security weaknesses for personal benefit, which can lead to serious financial losses, reputational damage, and privacy violations. Cybersecurity professionals continuously work to defend systems against such threats, making ethical hacking a crucial countermeasure.
Grey hat hackers exist in a middle ground between ethical and malicious hacking. They may access systems without explicit permission but often without harmful intentions. Sometimes they identify vulnerabilities and inform organizations afterward. However, even if their intentions aren’t malicious, unauthorized access can still raise ethical and legal concerns. This category shows how complex cybersecurity ethics can sometimes be.
One common mistake beginners make is trying to learn too many programming concepts or languages at the same time. This often leads to confusion and loss of confidence. The solution is to focus on one language and one concept at a time. Mastering the basics slowly creates a strong foundation and makes future learning easier.Another frequent mistake is skipping fundamental concepts and jumping straight into advanced topics. Beginners sometimes feel that the basics are too simple or boring, but ignoring them creates gaps in understanding. The solution is to spend enough time on core concepts, as they are the building blocks of everything that comes later in coding.
Hacktivists use hacking as a way to express political or social opinions. Their activities might include exposing information, defacing websites, or disrupting services to promote a cause. While some view hacktivism as activism, it can still involve legal risks and cybersecurity consequences.Understanding these categories helps clarify that hacking itself isn’t inherently good or bad intent, ethics, and legality define its impact.
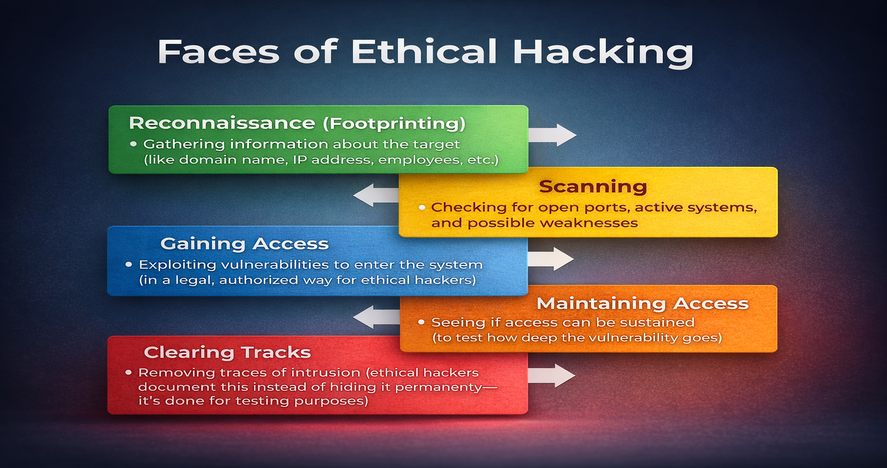
Ethical hacking is often misunderstood as random experimentation with tools and techniques. In reality, it follows a well-structured and professional methodology. Ethical hackers don’t “try things and see what happens.” They follow a planned process designed to identify weaknesses safely, legally, and responsibly. This structured approach ensures that testing strengthens security rather than disrupts operations.Each phase builds on the previous one, creating a complete picture of how secure or vulnerable a system truly is. Let’s break it down in a way that feels practical and real.
Every successful security assessment begins with understanding the target. In this initial phase, ethical hackers collect as much relevant information as possible about the system they are authorized to test. This may include publicly available data, domain details, server information, or general system architecture.Think of this phase as research before solving a problem. You wouldn’t attempt to fix something without understanding how it works. Ethical hackers analyze how a company’s digital infrastructure is structured what technologies are being used, how systems communicate, and where potential weak points might exist.Strong preparation at this stage makes the rest of the process more efficient. The more accurately a hacker understands the system, the easier it becomes to identify possible vulnerabilities later.
Once sufficient information has been gathered, the next step is to analyze the system more deeply. During scanning, ethical hackers look for technical weaknesses that could potentially be exploited. This might involve checking for outdated software, misconfigured servers, open ports, weak authentication mechanisms, or insecure network settings.This phase is about identifying cracks in the foundation. Systems are complex, and even small configuration errors can create security risks. Ethical hackers carefully evaluate these areas to determine where potential threats could arise.Vulnerability analysis helps prioritize risks. Not all weaknesses are equally dangerous. Some may pose minor concerns, while others could lead to serious breaches if exploited. Understanding this difference is crucial for improving security effectively.
After identifying vulnerabilities, ethical hackers test whether those weaknesses can actually be exploited. This is done carefully, within clearly defined limits, and always with proper authorization.The goal here is not to cause damage but to simulate what a real attacker might attempt. If a vulnerability exists, ethical hackers assess how far an unauthorized user could potentially go whether they could access sensitive data, modify information, or disrupt operations.This phase provides realistic insight into the actual risk level of a vulnerability. It transforms theoretical weaknesses into practical understanding. Organizations gain clarity on how serious a security gap truly is and what impact it might have if left unresolved.
Cyber attackers often try to remain undetected once they gain access to a system. Ethical hackers simulate this scenario to help organizations understand long-term security risks.This phase evaluates whether unauthorized access could persist over time. It also highlights weaknesses in monitoring systems, detection tools, or internal response strategies. By identifying gaps in these areas, organizations can strengthen their incident detection and response capabilities.Understanding persistence risks is important because preventing entry is only one part of cybersecurity. Detecting and responding quickly is equally critical.
Perhaps the most important phase of ethical hacking is reporting. Unlike malicious hackers, ethical hackers document everything they discover. They provide clear, structured reports that explain vulnerabilities, their potential impact, and recommended solutions.These reports are not just technical documents they serve as action plans for improvement. Organizations use them to patch vulnerabilities, update systems, improve configurations, and strengthen internal policies.This is where ethical hacking truly proves its value. The goal is not simply to “find flaws” but to help fix them. Security testing becomes meaningful only when it leads to measurable improvements.
Ethical hacking is professional, methodical, and responsible. Each phase from reconnaissance to reporting plays a vital role in strengthening cybersecurity defenses. Skipping steps or rushing the process can lead to incomplete assessments or overlooked vulnerabilities.By following a structured methodology, ethical hackers ensure testing remains controlled, effective, and beneficial. In a world where cyber threats continue to evolve, this disciplined approach is essential for building stronger and more resilient digital systems.

Ethical hacking is no longer a niche concept limited to tech circles it has become a core pillar of modern cybersecurity. As businesses move online and individuals depend on digital platforms for almost everything banking, shopping, communication, education protecting data is no longer optional. It’s essential.Ethical hackers play a quiet but powerful role behind the scenes. They help organizations identify weaknesses before cybercriminals can exploit them. From preventing financial fraud to protecting sensitive customer information, their work directly impacts digital trust. Without ethical hackers, the systems we rely on daily would be far more vulnerable to attacks.Major global technology companies like Google and IBM invest heavily in cybersecurity teams because even a small vulnerability can lead to massive financial loss, reputational damage, or data breaches. But ethical hacking isn’t just for big tech. It has become essential across industries banking, healthcare, education, e-commerce, startups, and government institutions all rely on cybersecurity professionals to safeguard their digital infrastructure.
Ethical hacking has very practical, real-world uses it’s not just theoretical testing in a lab.In the banking sector, ethical hackers help secure online transactions and digital payment systems, reducing the risk of fraud and unauthorized access. With the growth of digital wallets and online banking in countries like India, cybersecurity has become a critical priority.In healthcare, protecting patient data is extremely important. Hospitals and healthcare providers use cybersecurity testing to ensure medical records remain confidential and secure. A single breach could expose highly sensitive information, so preventive testing becomes crucial.E-commerce platforms depend on ethical hackers to protect customer payment information and maintain trust. If users feel their data isn’t safe, they simply won’t use the platform. Ethical hacking strengthens login systems, payment gateways, and backend databases to prevent misuse.Governments also rely on cybersecurity professionals to protect national digital infrastructure. Public service portals, digital identity systems, and communication networks all require continuous security assessments to defend against evolving cyber threats.Even for everyday internet users, ethical hacking makes a difference. When you use social media, shop online, stream content, or make digital payments, you benefit from security systems that have been tested and strengthened by ethical hackers. Their work creates safer online experiences that most people never even notice but rely on every day.

Starting a career in ethical hacking usually begins with understanding computer basics, networking concepts, and cybersecurity fundamentals. Learning operating systems, internet security principles, and problem-solving skills builds a strong foundation. Continuous learning is essential because technology and cyber threats evolve rapidly.Certifications can also help build credibility. Organizations such as the EC-Council provide structured training programs that introduce ethical hacking practices and industry standards. Practical experience, curiosity, and consistent learning often matter more than immediate expertise.
As digital transformation accelerates worldwide, cybersecurity demand continues to grow. Ethical hacking offers diverse career opportunities, competitive growth potential, and the satisfaction of contributing to digital safety. Beyond technical skills, it also requires responsibility, ethical awareness, and a commitment to protecting people and information in an increasingly connected world.
Becoming an ethical hacker isn’t just about learning a few tools or technical tricks it’s about developing a mindset focused on curiosity, responsibility, and continuous learning. Ethical hackers are essentially digital problem-solvers who look for weaknesses in systems before someone with harmful intent does. That means both technical knowledge and personal qualities matter equally.A strong understanding of computer networks is one of the most important skills. Knowing how data moves across systems helps you recognize where vulnerabilities might exist. Similarly, familiarity with operating systems like Windows, Linux, and server environments helps you understand how systems function behind the scenes. Many security issues happen due to misconfigurations or outdated software, so this knowledge becomes very practical. Programming basics are also helpful. You don’t need to become a software developer immediately, but understanding how code works helps you identify security flaws and automate tasks. Alongside technical skills, ethical hackers need analytical thinking, patience, attention to detail, and ethical responsibility. Since cybersecurity threats evolve constantly, staying updated through courses, communities, and certifications such as those offered by EC-Council helps maintain professional growth.At the end of the day, ethical hacking is as much about mindset as it is about skill. Curiosity, discipline, and integrity often matter more than simply knowing advanced tools.
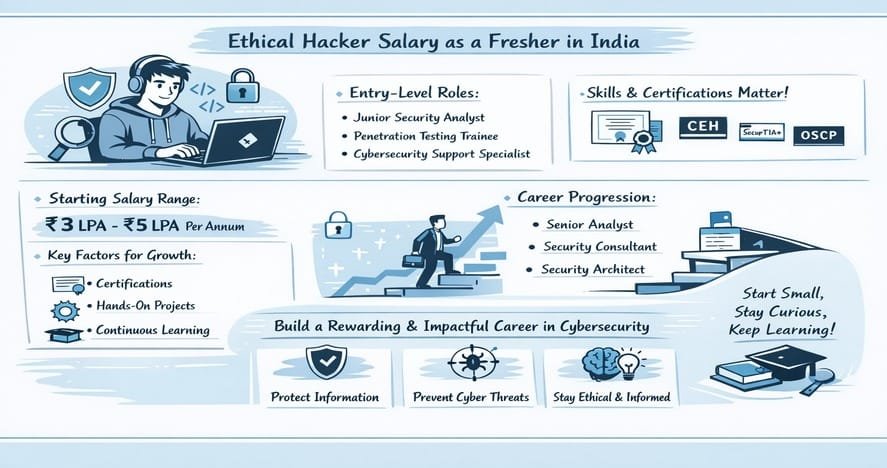
For beginners entering the cybersecurity field in India, salary expectations can vary depending on skills, certifications, company size, and location. Ethical hacking is considered a specialized IT skill, and with the rapid increase in cyber threats, companies across industries are investing heavily in digital security. This growing demand has created strong career opportunities for freshers who are willing to build the right skill set.On average, a fresher in ethical hacking can expect a starting salary between ₹3 LPA and ₹6 LPA in small to mid-sized companies. In larger IT firms, multinational corporations, or product-based companies, the starting package can range from ₹6 LPA to ₹10 LPA, especially if the candidate has strong practical knowledge and relevant certifications. Metropolitan cities like Bangalore, Hyderabad, Pune, Chennai, and Mumbai often offer slightly higher salaries due to higher demand and cost of living.Freshers typically begin their careers in roles such as junior security analyst, penetration testing trainee, or SOC (Security Operations Center) analyst. These positions focus on monitoring security systems, identifying vulnerabilities, supporting senior security professionals, and gaining hands-on exposure to real-world cybersecurity challenges. The initial years are crucial for building technical depth and understanding how organizations defend against cyber attacks.Several factors influence a fresher’s salary in ethical hacking. Practical skills in networking, operating systems, and basic scripting are highly valued. Hands-on experience through labs, internships, or participation in bug bounty programs can significantly improve employability. Certifications from recognized organizations like EC-Council and CompTIA also strengthen a candidate’s profile, although skills and practical exposure remain more important than certificates alone.Continuous learning plays a major role in salary growth. Cybersecurity is a rapidly evolving field, and professionals who stay updated with new tools, threats, and defensive strategies tend to progress faster. With two to three years of experience, salaries often increase substantially, andprofessionals may move into higher-paying roles such as penetration tester, security consultant, or senior analyst. Over time, experienced ethical hackers can advance to leadership or specialized technical positions with significantly higher compensation.Overall, ethical hacking offers promising long-term growth in India. While starting salaries may vary, the field rewards dedication, consistent skill development, and adaptability. For freshers who are passionate about cybersecurity and committed to learning, career progression and earning potential can be highly rewarding.

Ethical hacking isn’t just about technology it’s about responsibility, awareness, and contributing to a safer digital environment. As our dependence on digital platforms continues to grow, the need for cybersecurity professionals becomes increasingly important. Ethical hackers play a key role in protecting sensitive information, preventing cyber threats, and building trust in technology.If you’re considering this path, start simple. Focus on fundamentals, stay curious, and don’t compare your progress to others. Every expert was once a beginner. Consistent learning, practical exposure, and ethical awareness will shape your journey more than shortcuts ever will.Ethical hacking offers not only strong career opportunities but also meaningful impact. Protecting digital systems means protecting people, businesses, and information. With patience, dedication, and the right mindset, you can build a career that is both professionally rewarding and socially valuable.